Current routers with voip have built-in STUN. Because of this they can effectively bypass the NAT mechanisms. STUN abbreviation can be deciphered as Simple Traversal of UDP through NATs, which means "easy circumvention of UDP through NAT".
This protocol helps to route packets of devices that are outside the NAT. This is a very useful thing, but at the same time, it is not a panacea for all the problems that are related to NAT firewalls.
Operating principle
Many protocols use UDP-packages when sending voice traffic and text or graphical content over IP-networks. However, when the two devices involved in the transmission of data do not fall into the action zone of NAT, it is impossible to establish a connection between them in a standard way. These are situations when STUN is of help.
It is a client-server Internet Protocol. It works based on the interaction of STUN-client (the object that generates requests) and a STUN-server (the object that receives requests and sends responses). The client sends a request to the STUN-server. The latter sends information on the NAT firewall address, as well as on which port is currently open for requests in the IP- network. In addition, data on the type of broadcast address are sent.
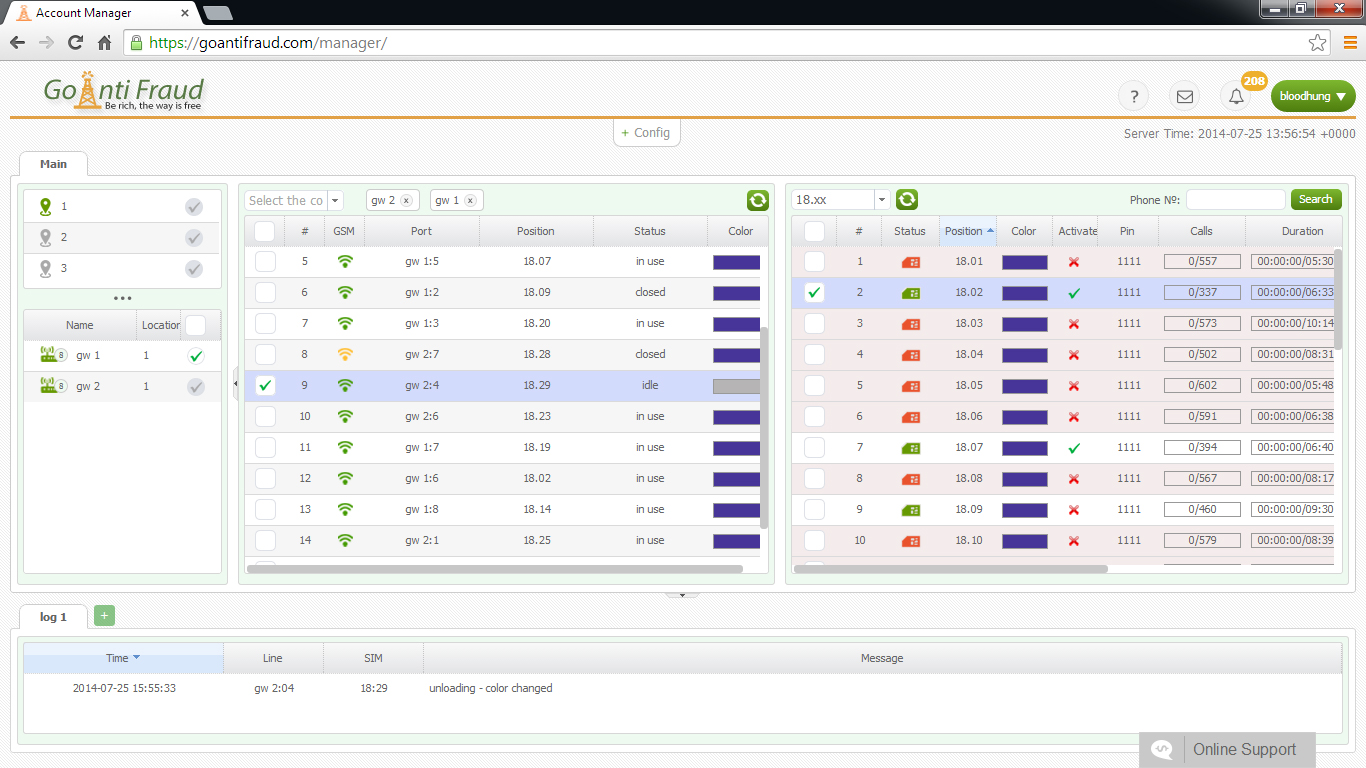
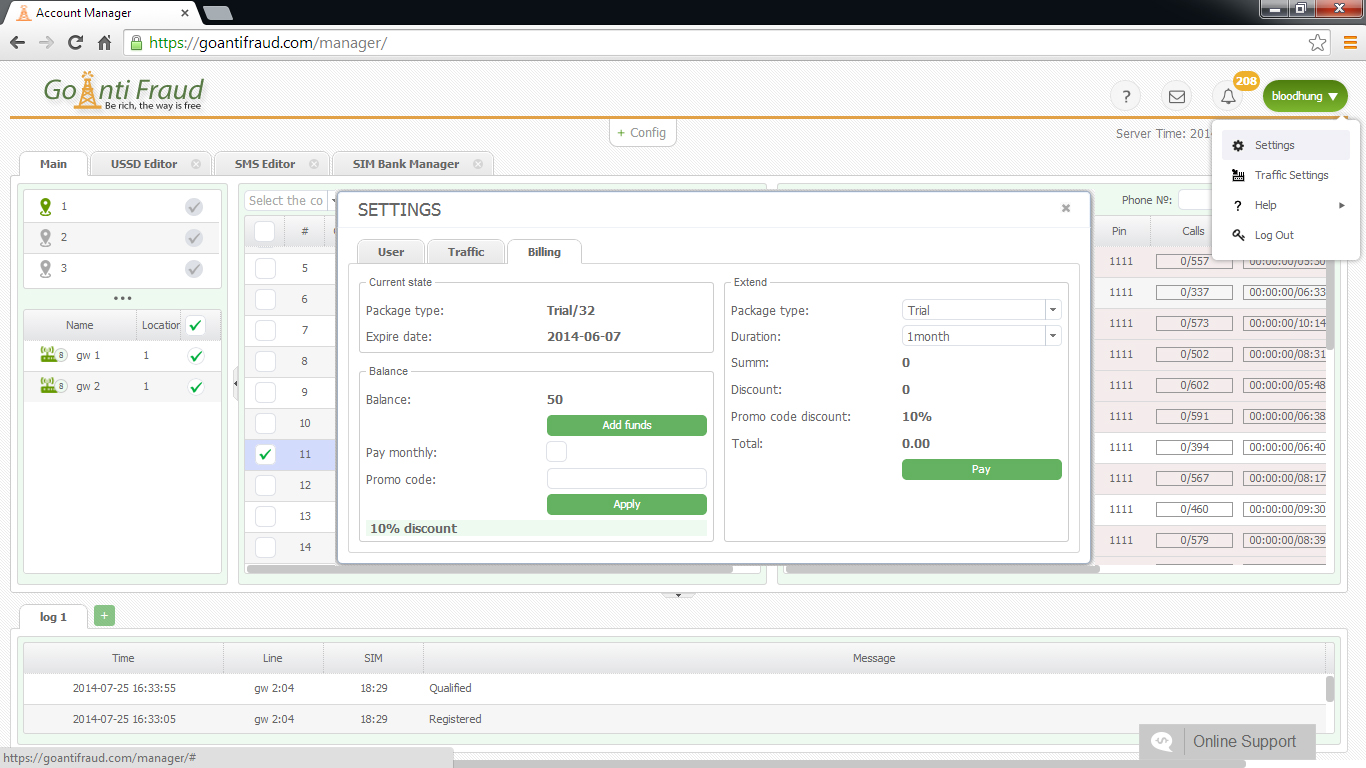
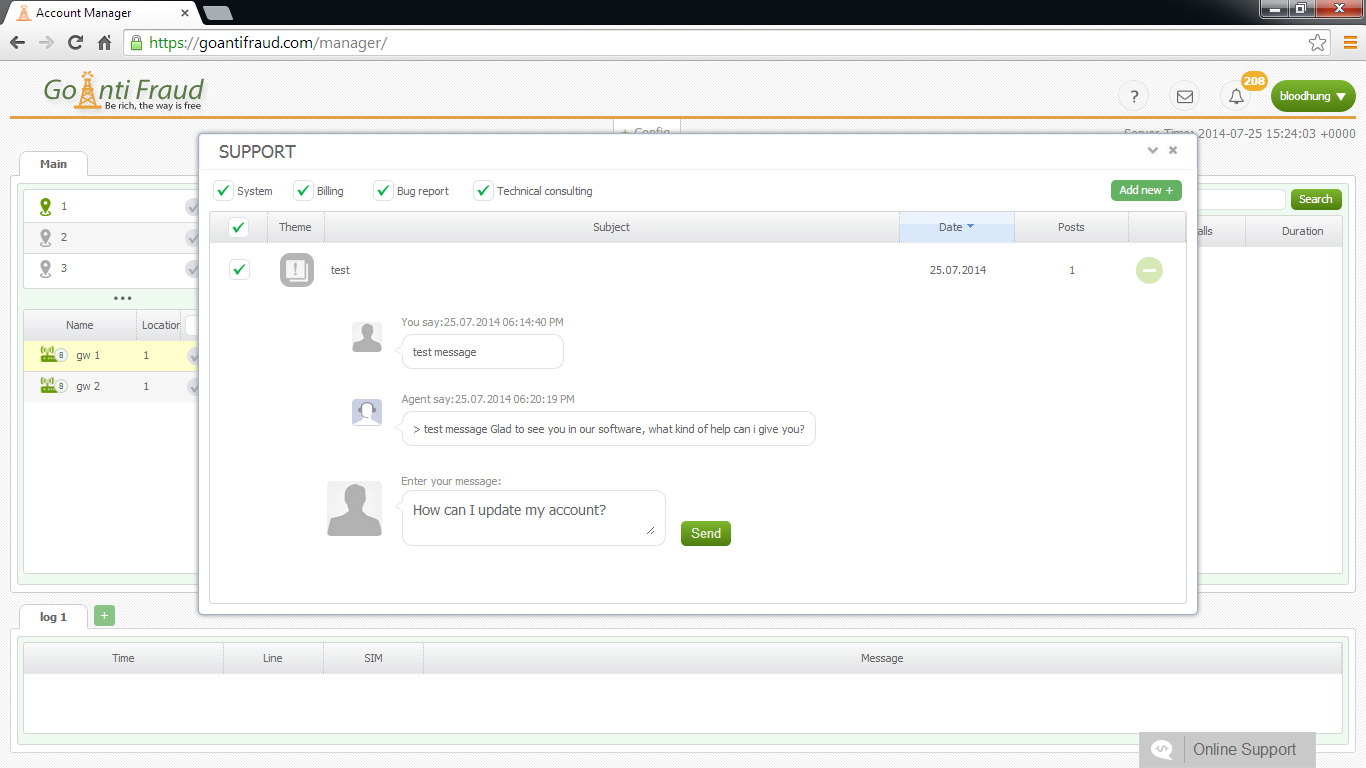
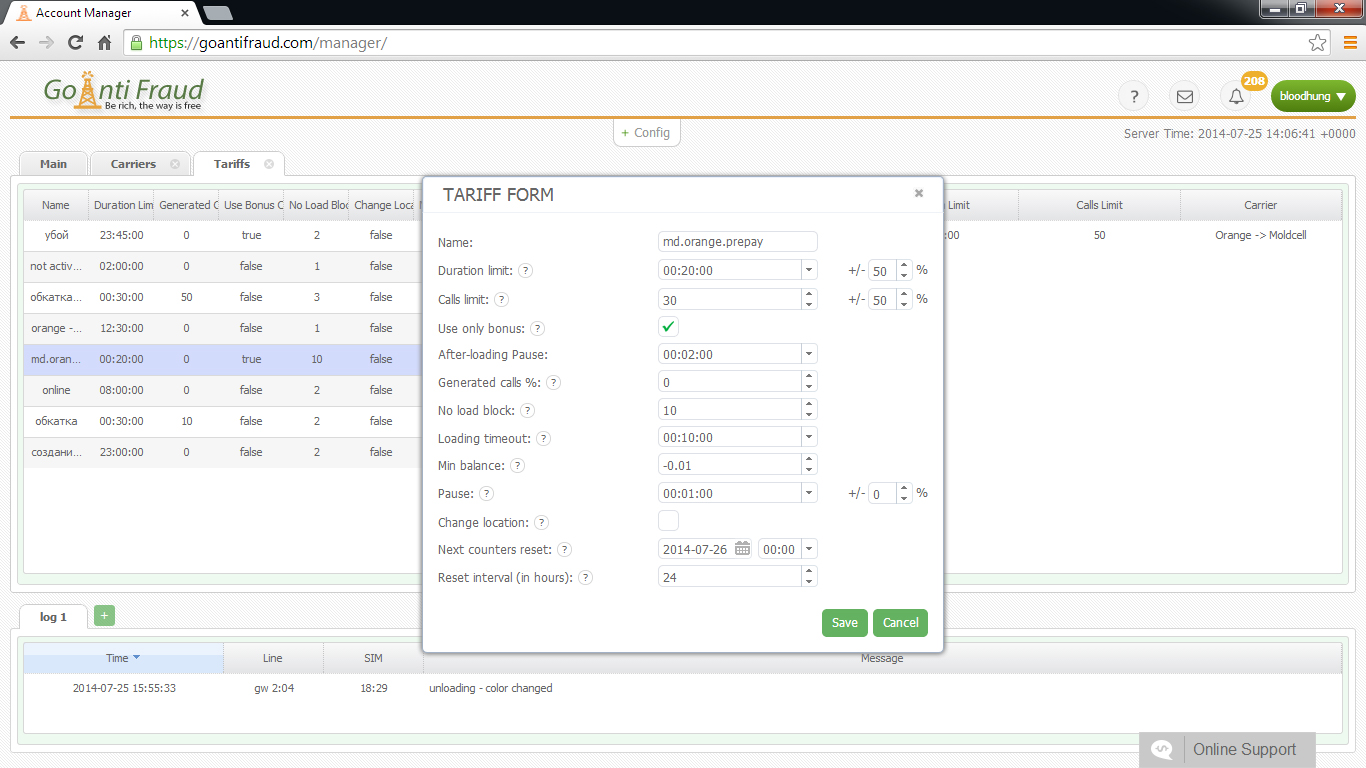
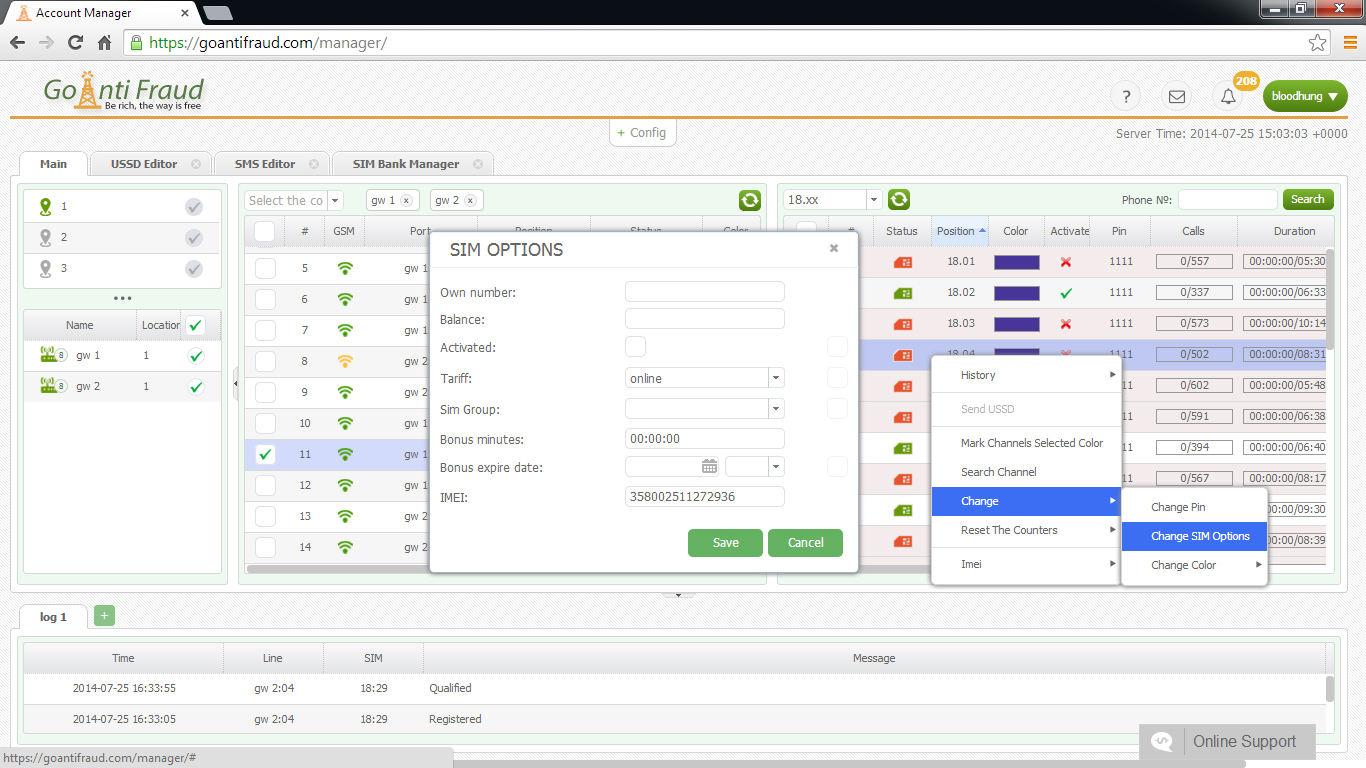
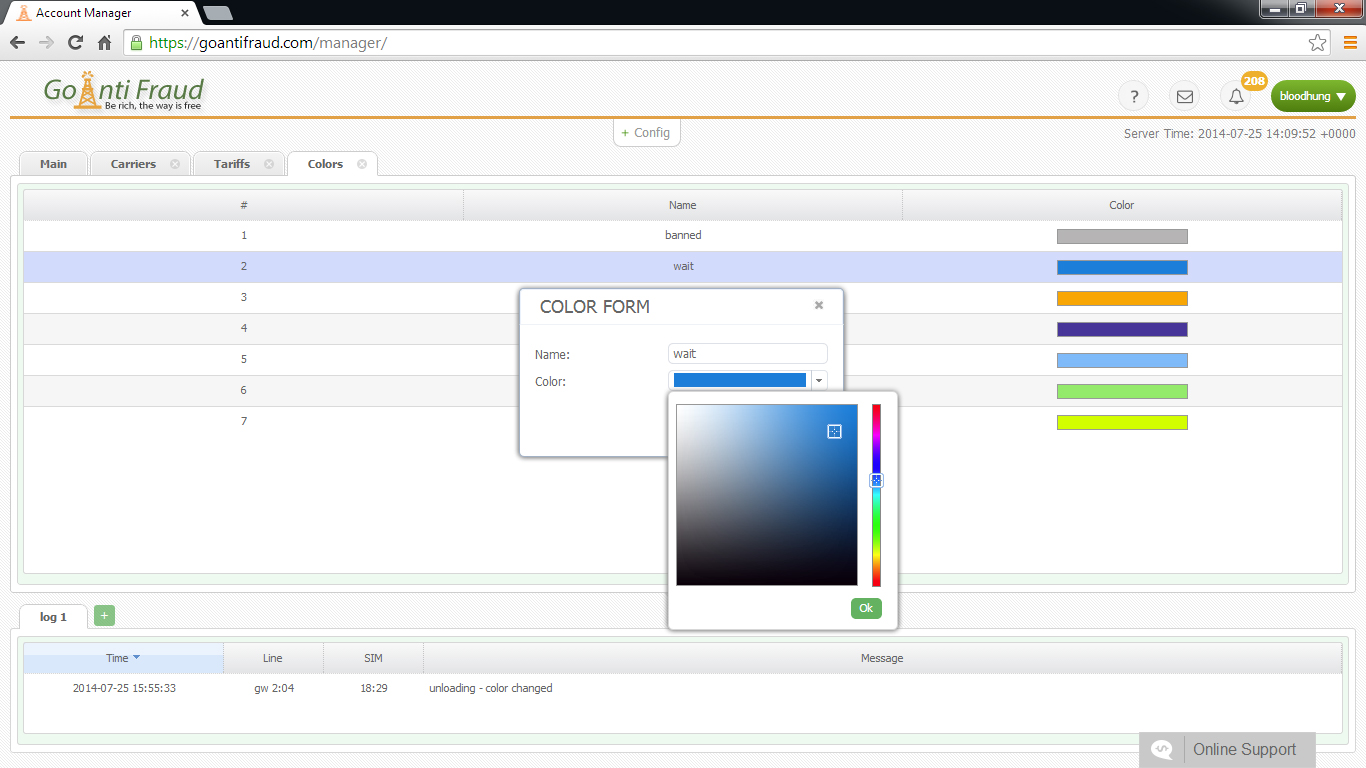
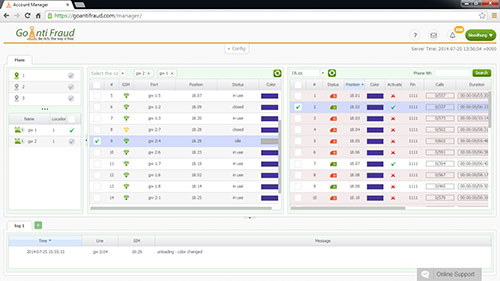
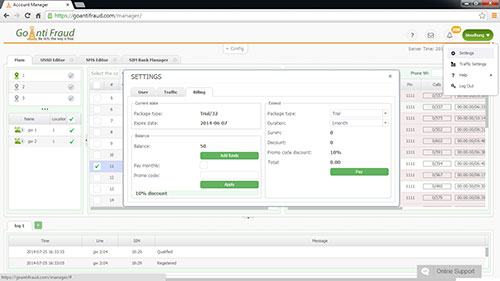
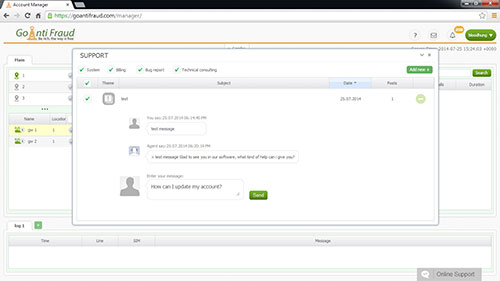
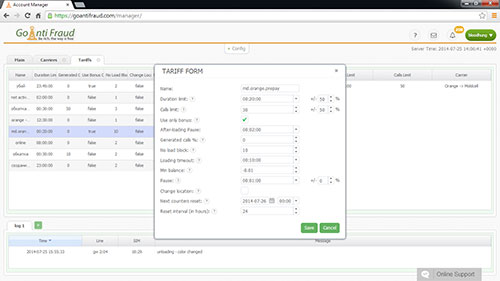
Are you interested in VoIP technology? Are you looking for a reliable start-up in the telecommunications sector? You will be interested in the opportunity to start a GSM termination business. You can get the maximum profit making the minimal investment! We offer a turnkey GoAntiFraudsolution for beginners , which includes opportunities for efficient VoIP termination, as well as a set of equipment by GoIP, EjoinTech & China Skyline at low cost.
Different firewalls/routers process UDP packages in various ways. The STUN protocol usually works with four types of NAT:
- Full Cone;
- Symmetric;
- Adress Restricted;
- Port Restricted.
How the connection is established
The client and the server are connected via TCP / UDP of the port 3478. At the same time, the STUN proposes that the client check another address and port number (as STUN is tied directly to the two IP-addresses). Usually, selection of ports and addresses occur in any mode. The protocol often uses DNS SRV records to locate STUN servers connected to the domain.
Currently, VoIP devices have no universal support by the STUN protocol. Since 2015, it is provided by default, but it is not available in the outdated devices.
This VoIP protocol has some disadvantages. For example, ite cannot properly work in IP- networks, which use Symmetric NAT, since the latter is constantly creating new addresses and ports when an internal host is trying to connect to an external voip gateway.
GoAntiFraud offers you to start a profitable GSM termination business ! If you are interested in VoIP technology, we will help you start your own business, yielding a stable income. By purchasing our comprehensive New Business package, you will start making money immediately! We will give you full technical support at all stages of business.